Security in both IMS and EPC, is a broader subject that involves different aspects and mechanisms developed by the Internet and wireless communities and finally ended within the hands of IETF and 3GPP standardization bodies. Throughout this post, we will try to elaborate on the subject of Authentication and Key Agreement mechanism in IMS, EPC/MME (3GPP) and EPC/ePDG (non-3GPP). A mandatory initial process that needs to be fulfilled before any Wireless User is granted access to legacy services like CS/PS (circuit switched/GPRS), IMS services or both. The AKA in IMS and EPC are pretty much similar, however, the Network elements involved , the transport layers and payload carrier protocols might differ according to the type of technology and Wireless operators policies. Furthermore AKA in both EPC/UMTS and IMS uses a symmetric cryptography and a challenge-response based mechanism. Though, recently an additional resiliency has been added to the IMS AKA mechanism by introducing a mapping of AKA parameters to an HTTP Digest authentication scheme. According to RFC 3310 “this mapping enables the usage of AKA as a one-time password generation mechanism for Digest authentication.”
The following are the main standard documents dealing with Security and AKA in EPC and IMS: TS 33.102, TS 33.203 and RFC 3310
The UICC is a smart card like device on top of which resides both the USIM and ISIM modules. First, the EPC (LTE IP-CAN) AKA runs on the USIM (UMTS Services Identity Module) at the wireless Subscriber/User level and on the EPC-HSS/HLR at the Subscriber Home Network level. Second, the Wireless and internet convergence urged the Wireless operators to consider WiFi access (non-3GPP IP-CAN) as a fall back for LTE. The AKA for WiFi (non-3GPP access) is pretty similar to EPC-LTE (3GPP access), however, the EAP protocol is used for Authentications and HTTP as a carrier. Finally, the ISIM (IMS Services Identity Module) hosts the User Equipment (Wireless User) IM AKA and the IMS-HSS (Home Subscriber Server) hosts the IMS AKA functions and mechanisms at the Home network level.
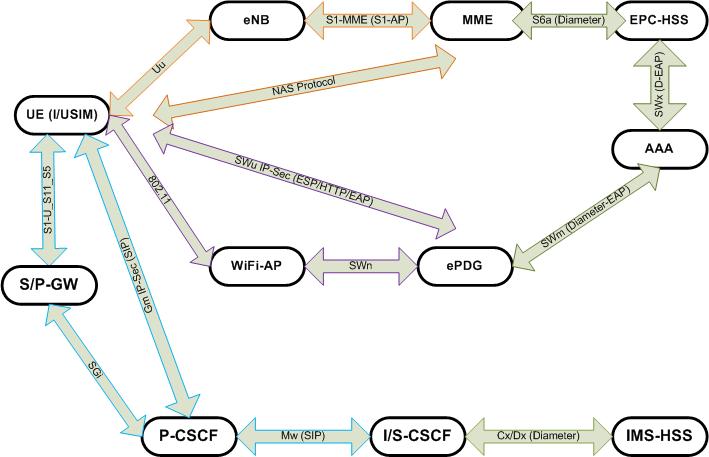
In addition to UE level (ISIM/USIM) and Network level (HSS/HLR/AAA) as persistent AKA parameters storage, different Network elements are involved in the fulfillment of AKA for EPC/LTE, EPC/WiFi and IMS. The S-CSCF plays the intermediary role between the HSS and UE in case of IMS AKA. The MME takes the lead for EPC/LTE AKA and position itself as the median challenger and checker. Finally, the ePDG plays the same role for non-3GPP WiFi access AKA. In contrast to the first two cases where both S-CSCF and MME are directly (logically) connected to HSS, the ePDG is reaching to HSS through an intermediary AAA server.
The following are the main standard documents dealing with Security and AKA in EPC and IMS: TS 33.102, TS 33.203 and RFC 3310
- STORAGE OF THE AKA PARAMETERS
The UICC is a smart card like device on top of which resides both the USIM and ISIM modules. First, the EPC (LTE IP-CAN) AKA runs on the USIM (UMTS Services Identity Module) at the wireless Subscriber/User level and on the EPC-HSS/HLR at the Subscriber Home Network level. Second, the Wireless and internet convergence urged the Wireless operators to consider WiFi access (non-3GPP IP-CAN) as a fall back for LTE. The AKA for WiFi (non-3GPP access) is pretty similar to EPC-LTE (3GPP access), however, the EAP protocol is used for Authentications and HTTP as a carrier. Finally, the ISIM (IMS Services Identity Module) hosts the User Equipment (Wireless User) IM AKA and the IMS-HSS (Home Subscriber Server) hosts the IMS AKA functions and mechanisms at the Home network level.
- NETWORK ELEMENTS, INTERFACES and PROTOCOLS
In addition to UE level (ISIM/USIM) and Network level (HSS/HLR/AAA) as persistent AKA parameters storage, different Network elements are involved in the fulfillment of AKA for EPC/LTE, EPC/WiFi and IMS. The S-CSCF plays the intermediary role between the HSS and UE in case of IMS AKA. The MME takes the lead for EPC/LTE AKA and position itself as the median challenger and checker. Finally, the ePDG plays the same role for non-3GPP WiFi access AKA. In contrast to the first two cases where both S-CSCF and MME are directly (logically) connected to HSS, the ePDG is reaching to HSS through an intermediary AAA server.
The interfaces and protocols involved in AKA are different too. The IMS AKA is carried out through Gm interface (UE <->P-CSCF) where SIP (Session Initiation Protocol) is the carrier of AKA parameters and IP-Sec guarantees the Confidentiality and Integrity protection of the payload. Mw interface (P-CSCF <-> S-CSCF) and we need to mention the role of I-CSCF as the entry point to a domain, responsible for User Authorization through Cx (Diameter) and S-CSCF selection. Again SIP takes the responsibility of carrying the AKA parameters at the Mw interface reference point using plain TCP/UDP transport and a security layer might/might not be needed according to operator policies. The last and not least interface involved in IMS AKA is the Cx interface (S-CSCF <->HSS) and Diameter is the protocol running on this interface through which S-CSCF fetches Authentication vectors to be exchanged for Mutual authentication UE <-> IMS Core.
The EPC/LTE AKA operations are accomplished through different standard interfaces and protocols. The NAS (Non Access Stratum) protocol takes the carrier role of AKA parameters between UE and MME. The different transport and lower layer functions at Uu interface (UE<->eNB) and S1-MME interface (eNB <->MME) are not very important to the subject under discussion (AKA). The Diameter Protocol runs on top of the S6a interface (MME <-> EPC-HSS). Through this interface, the MME fetches the Authentication vectors (AVs) to be exchanged later on for mutual authentication between UE <-> EPC core. An additional security mechanism through S13 interface between MME and EIR is worth mentioning even though it is not very important to our subject.
The EPC/WiFi AKA is based on a 3GPP adopted IETF standard EAP-AKA that follows the same EPC/LTE and IMS model, however, the interfaces and protocols differs. IP-SEC takes the responsibility of Integrity and confidentiality of the information exchanged at the SWu interface (UE <->ePDG) whereas HTTP protocol carries the AKA parameters in the form of ESP. Diameter protocols runs on top of both SWm interface (ePDG <->AAA) and SWx interface (AAA<->EPC-HSS). Similarly to IMS and EPC/LTE cases, ePDG fetches the Authentication Vectors (AVs) to be exchanged between UE and EPC core for mutual authentication.
The bottom line of the AKA process is the mutual authentication between the Home network domain (HSS/AuC) and the user/subscriber domain (USIM/ISIM). Both domains are provisioned with a Pre-shared Key (K) for an additional security layer on top of the Challenge/Response mechanism. HSS/AuC generates the AKA parameters in the form of Authentication Vectors (AVs) and distribute them, on demand, to the Serving Network elements. S-CSCF is the serving Network element for IMS, MME is for EPC/LTE and ePDG/AAA for LTE/WiFi. Authentication Vectors (AVs) include a random unpredictable value (RAND), an expected response (XRES), a ciphering Key (CK), an integrity key (IK) and an authentication token (AUTH). The Home domain grants services to User domain upon successful AKA. Therefore upon service request, the Serving Network (SN) relays the AKA parameters between the user and Network domain authenticators (USIM/ISIM and HSS/AuC) for Mutual Authentication.
The EPC/LTE AKA operations are accomplished through different standard interfaces and protocols. The NAS (Non Access Stratum) protocol takes the carrier role of AKA parameters between UE and MME. The different transport and lower layer functions at Uu interface (UE<->eNB) and S1-MME interface (eNB <->MME) are not very important to the subject under discussion (AKA). The Diameter Protocol runs on top of the S6a interface (MME <-> EPC-HSS). Through this interface, the MME fetches the Authentication vectors (AVs) to be exchanged later on for mutual authentication between UE <-> EPC core. An additional security mechanism through S13 interface between MME and EIR is worth mentioning even though it is not very important to our subject.
The EPC/WiFi AKA is based on a 3GPP adopted IETF standard EAP-AKA that follows the same EPC/LTE and IMS model, however, the interfaces and protocols differs. IP-SEC takes the responsibility of Integrity and confidentiality of the information exchanged at the SWu interface (UE <->ePDG) whereas HTTP protocol carries the AKA parameters in the form of ESP. Diameter protocols runs on top of both SWm interface (ePDG <->AAA) and SWx interface (AAA<->EPC-HSS). Similarly to IMS and EPC/LTE cases, ePDG fetches the Authentication Vectors (AVs) to be exchanged between UE and EPC core for mutual authentication.
- THEORY: MUTUAL AUTHENTICATION USER <->NETWORK
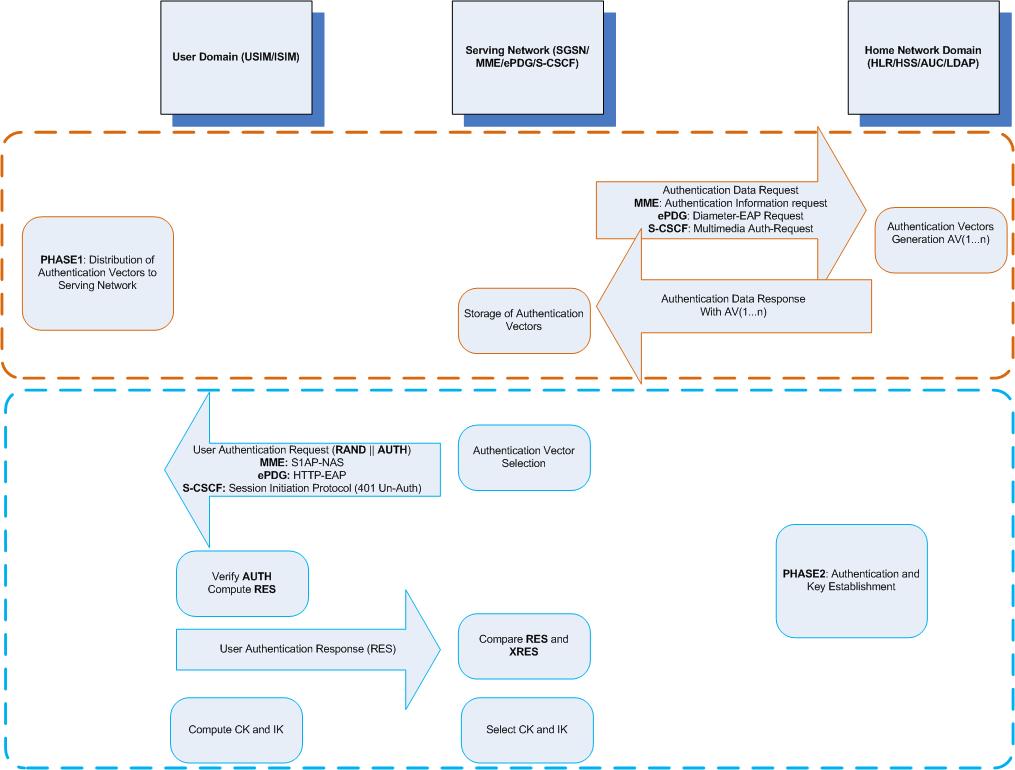
The bottom line of the AKA process is the mutual authentication between the Home network domain (HSS/AuC) and the user/subscriber domain (USIM/ISIM). Both domains are provisioned with a Pre-shared Key (K) for an additional security layer on top of the Challenge/Response mechanism. HSS/AuC generates the AKA parameters in the form of Authentication Vectors (AVs) and distribute them, on demand, to the Serving Network elements. S-CSCF is the serving Network element for IMS, MME is for EPC/LTE and ePDG/AAA for LTE/WiFi. Authentication Vectors (AVs) include a random unpredictable value (RAND), an expected response (XRES), a ciphering Key (CK), an integrity key (IK) and an authentication token (AUTH). The Home domain grants services to User domain upon successful AKA. Therefore upon service request, the Serving Network (SN) relays the AKA parameters between the user and Network domain authenticators (USIM/ISIM and HSS/AuC) for Mutual Authentication.
The AKA process consists of two phases: the distribution of Authentication vectors from HSS/AuC to the Serving Network elements and the Authentication and key establishment. A service request from unauthenticated user triggers the Serving Network (SN) to send an “Authentication Data Request” to fetches at least one Authentication vector from HSS/AuC. At this level, there is some kind of implicit trust between the HSS/AuC and the Serving network elements to secure the AKA parameters and fulfill the next phase. The Serving Network element sends an Authentication Request with Challenge (RAND) and AUTH parameters the User Domain authenticator. The user later (USIM/ISIM) Calculated the XMAC (expected Message Authentication Code) and compares it to the MAC value included in AUTH (SQN+MAC+AF) token from SN. If the values match, the User domain has accomplished the Authentication of the network. Furthermore, the User domain uses the Challenge (RAND) to compute a response (RES) value to include in the Authentication response to SN. If the XRES, received in the distribution phase matches the value the User domain computed, the Network domain has accomplished the authentication of User domain and services might be granted. At this stage both CK and IK are computed at the User domain level and a secure medium is established between the User and Network domains.
####### IMS AKA #######
IMS Authentication Vector Distribution
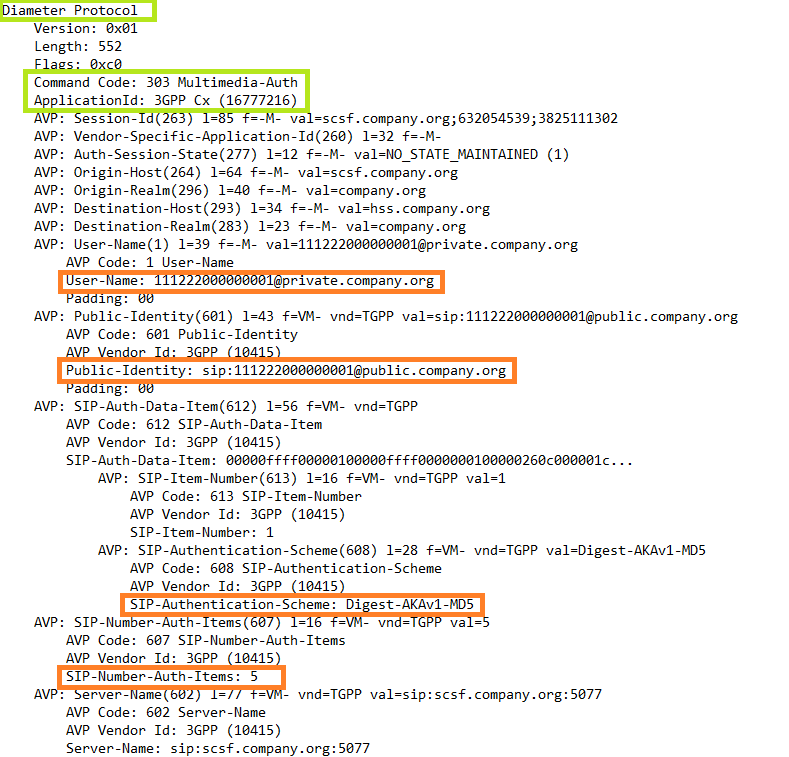
Multimedia Auth-Request Cx (S-CSCF --> HSS)
- AKA IN PRACTICE
####### IMS AKA #######
IMS Authentication Vector Distribution
Multimedia Auth-Request Cx (S-CSCF --> HSS)
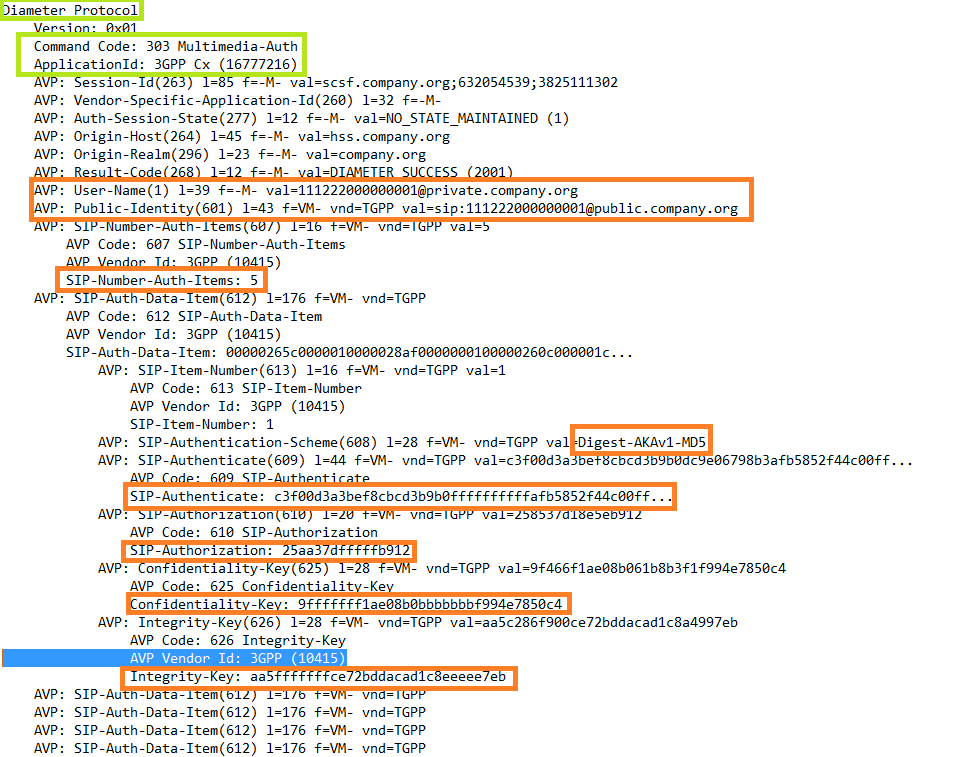
Multimedia Auth-Response Cx (HSS --> S-SCCF)
IMS Authentication and Key establishment
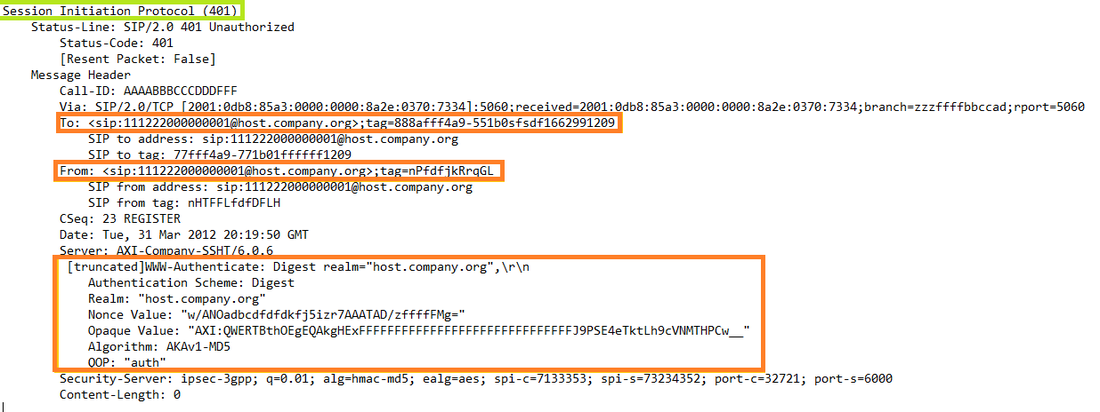
SIP 401-Unauthorized (S-CSCF --> P-CSCF --> UE)
SIP 401-Unauthorized (S-CSCF --> P-CSCF --> UE)
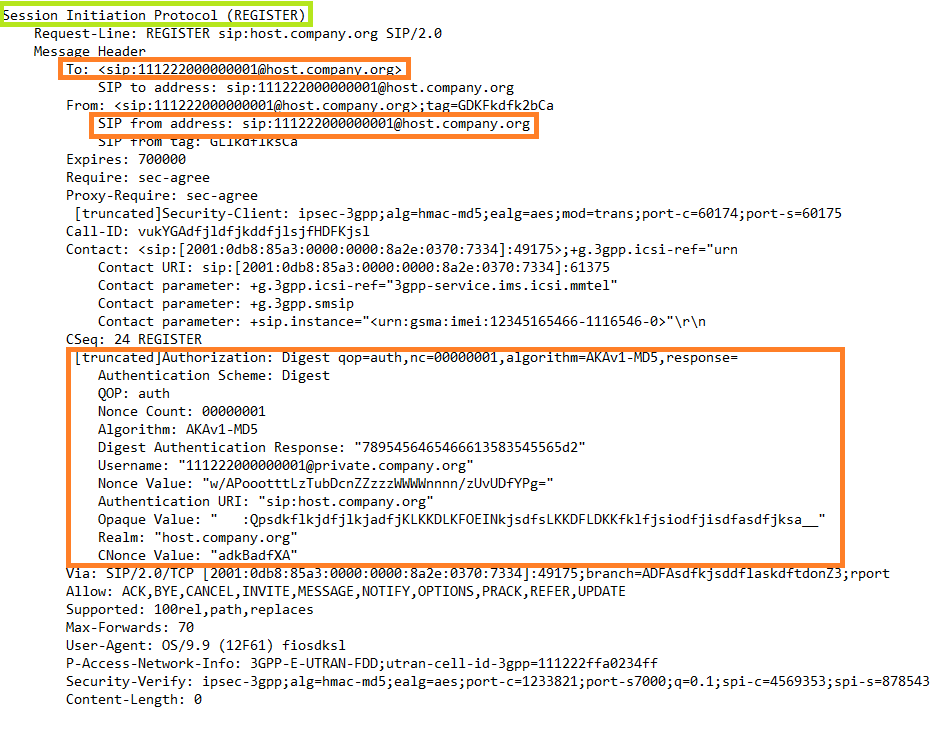
SIP REGISTER (UE --> P-CSCF --> S-CSCF)
###### EPC/WiFi AKA ######
EPC-WiFi Authentication vector Distribution
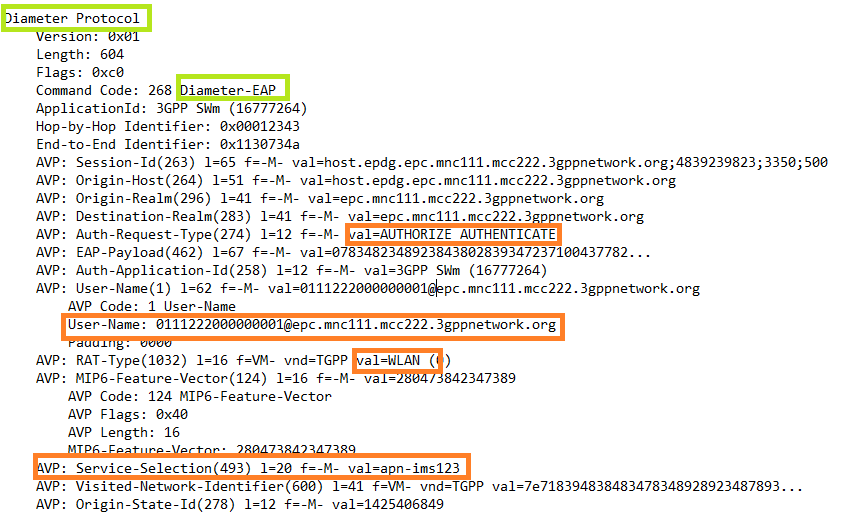
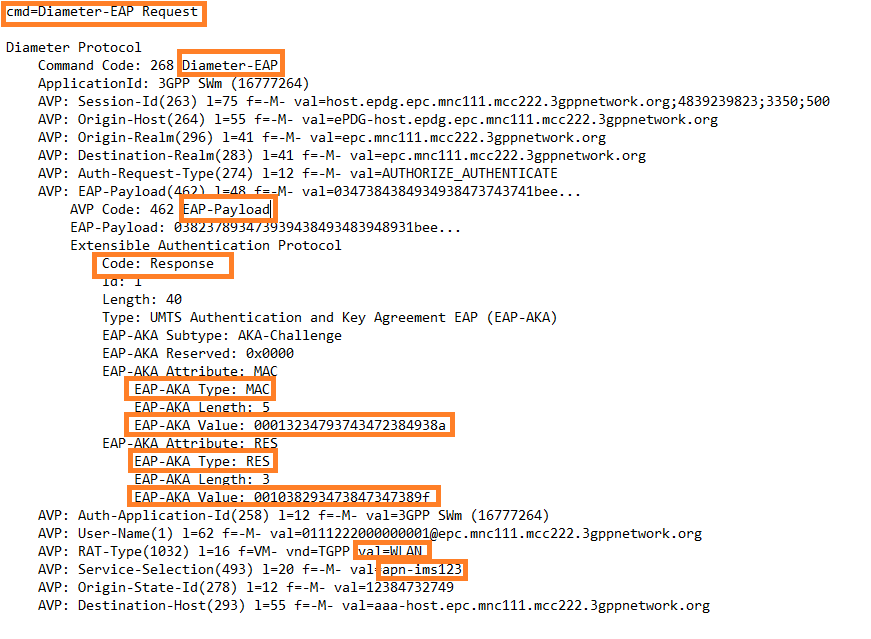
Diameter-EAP Request (ePDG <-> AAA)
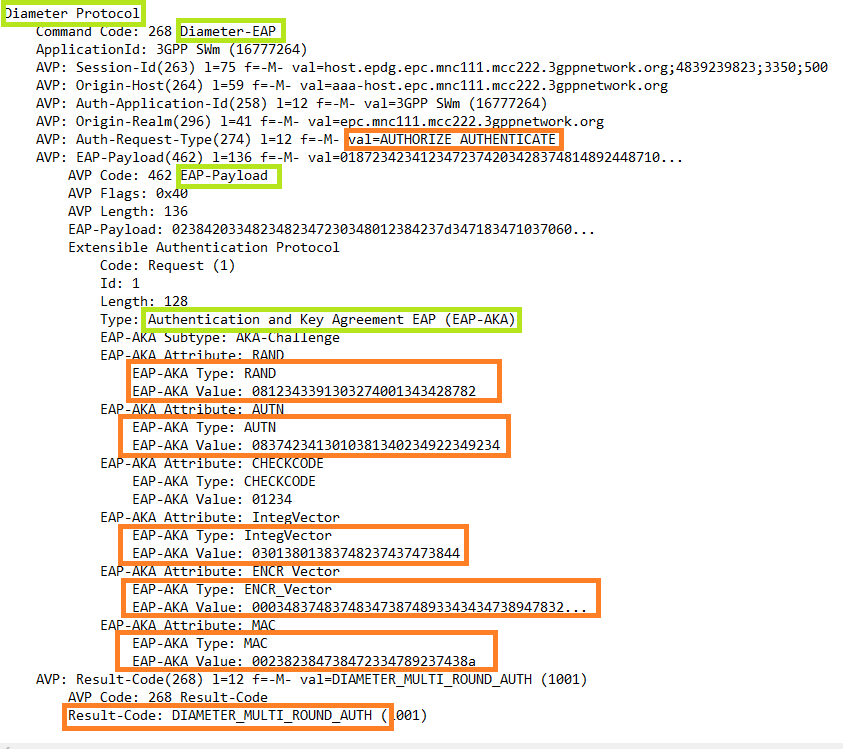
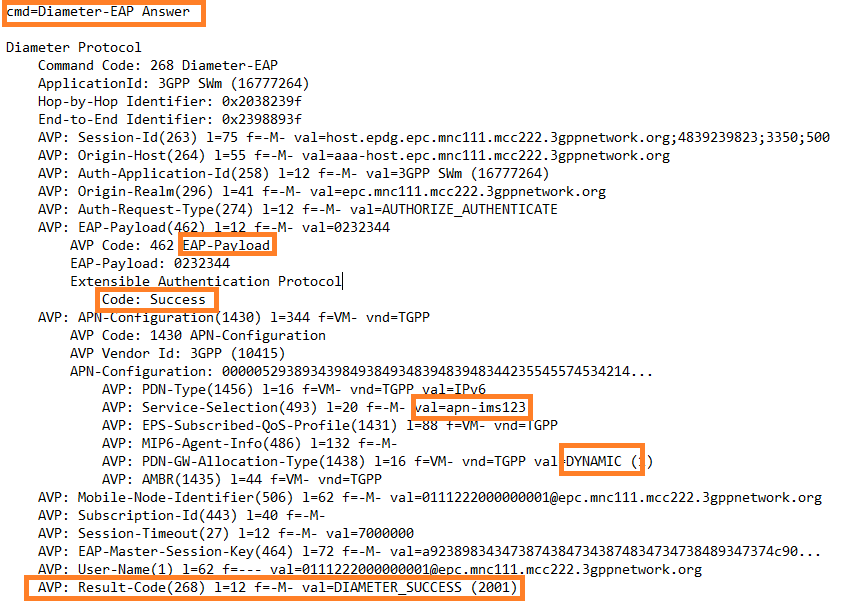
Diameter-EAP Answer (AAA <-> ePDG)
EPC-WiFi Authentication and Key establishment
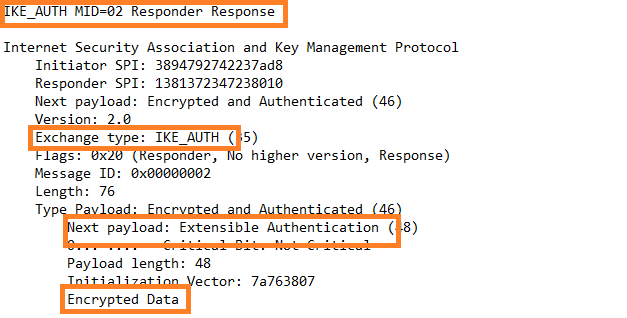
ePDG -> UE IKE_AUTH Response (Encrypted through ipSec Tunnel)
ePDG -> UE IKE_AUTH Response (Encrypted through ipSec Tunnel)
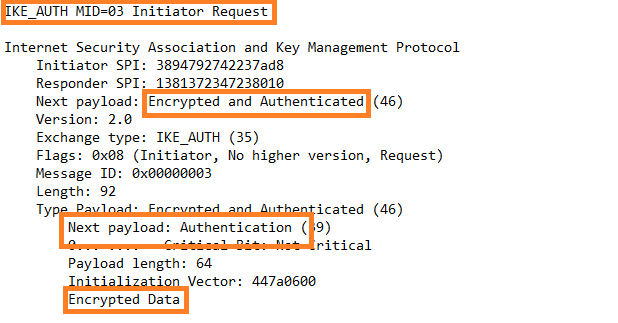
UE-> ePDG IKE_AUTH Request (Encrypted through ipSec Tunnel)
Unlike IMS and LTE-EPC Authentication and Key Establishment, the UE authentication check point is AAA, so the response received from the UE as a result of a challenge is forwarded to AAA for validation. If the authentication is successful, the subscriber profile, including the APN configuration list, is transferred to ePDG.
Diameter-EAP Request (ePDG <-> AAA)
Diameter-EAP Request (ePDG <-> AAA)
Diameter-EAP Answer (AAA <-> ePDG)
####### EPC-LTE AKA #######
EPC Authentication Vector distribution
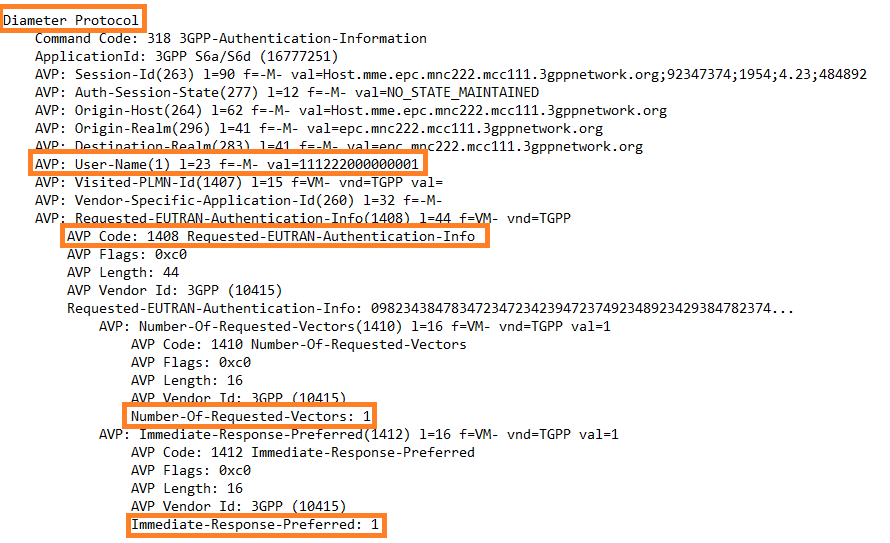
Authentication Information Request (MME <->HSS-EPC)
EPC Authentication Vector distribution
Authentication Information Request (MME <->HSS-EPC)
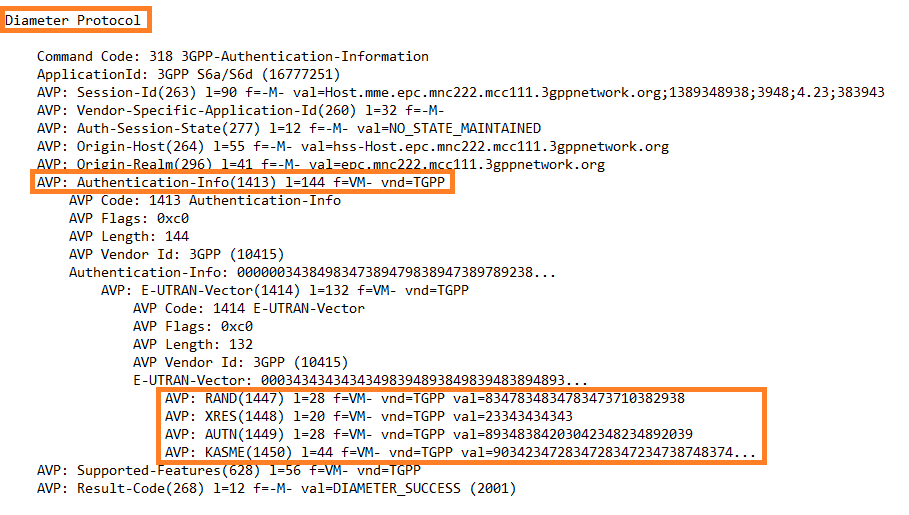
Authentication Information Answer (HSS-EPC <-> MME)
EPC-LTE Authentication and Key establishment
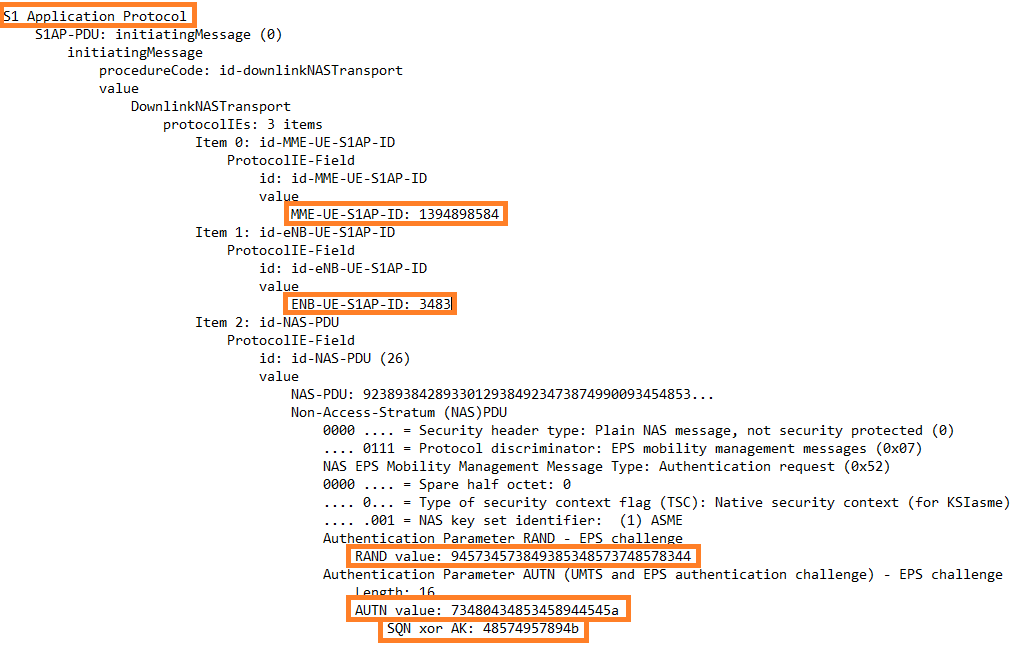
Authentication Request (MME <-> UE)
Authentication Request (MME <-> UE)
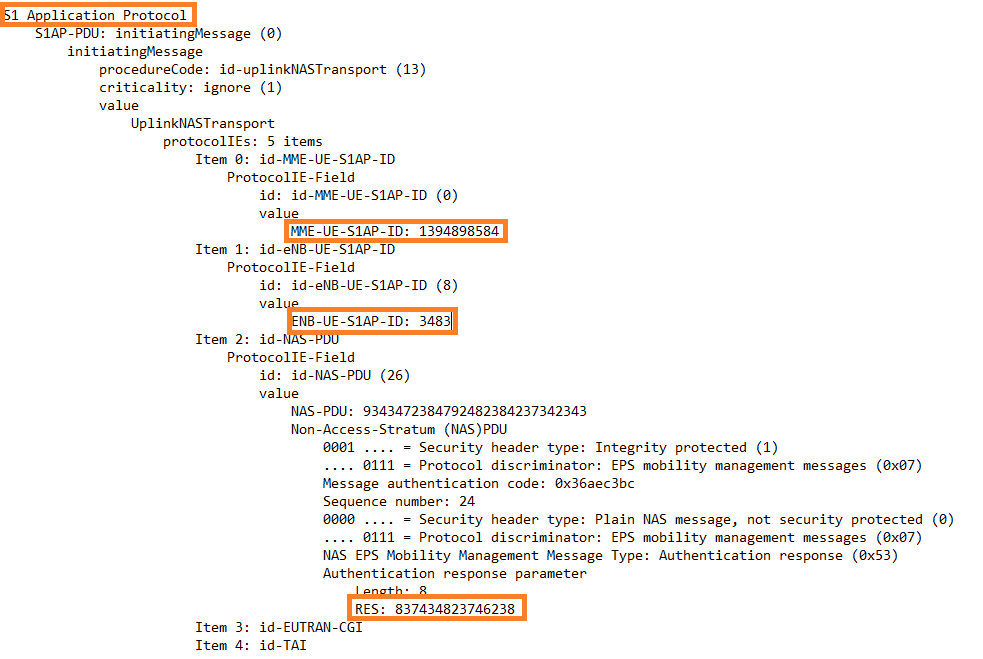
Authentication Response (UE <-> MME)
 RSS Feed
RSS Feed
